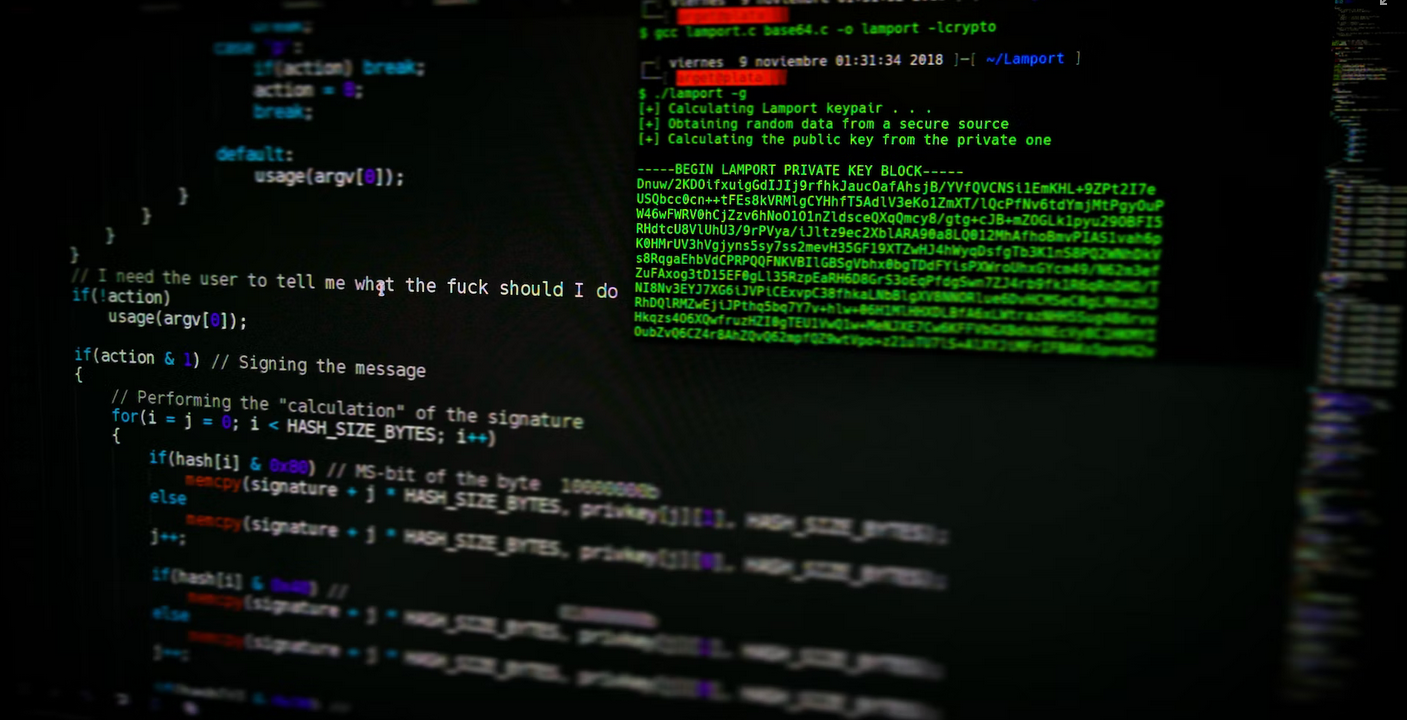
Why penetration testing is an important part of IT security
In the IT world, you would be able to see penetration testing to have become one of the most important concepts. This is because this could be used to assess and identify possible vulnerabilities in order to ensure the security of information, along with confidential data pertaining to technology.
Hence, for those people who do not seem to know much about what penetration testing is, a testing procedure that is typically used to identify possible vulnerabilities or risks that a particular network would face. It would successfully be able to point out the areas from which the illegal or unauthorized access could be obtained that could then destroy the reputation or credibility of a business environment.
In other words, penetration testing could mainly be used to identify and examine all the possible points of vulnerabilities that a company could face within its computer networks.
The importance of penetration testing in the IT world
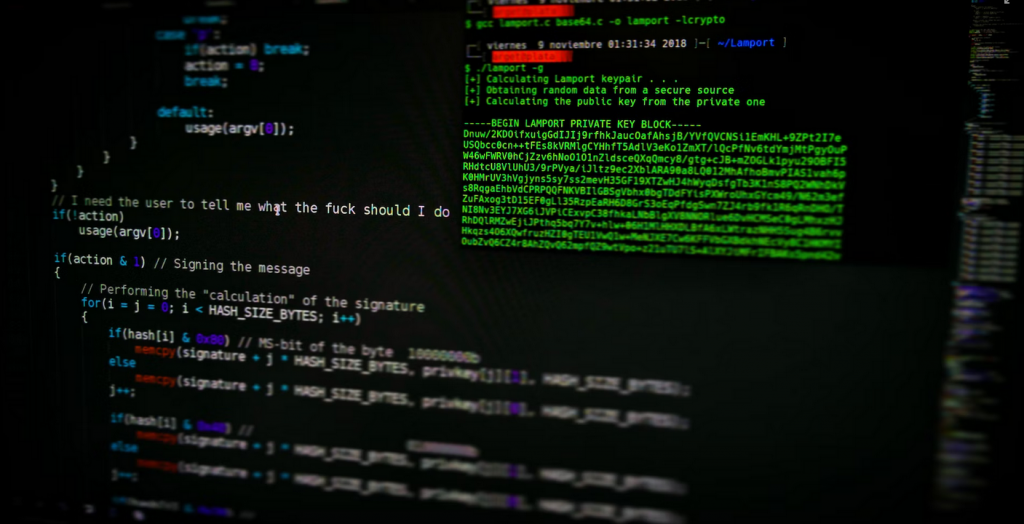
In the modern day and age, ethical hacking seems to have become quite famous, not only to determine the breach of security but also to propose the best solutions for an organization’s computer network systems. As a result, ethical hackers would be able to identify or determine the possible drawbacks or vulnerabilities that would seem to exist in computer networks.
As a result, an ethical hacker would be responsible for collecting all the necessary information of the hacking results. This would be done to ensure that the security of computer networks would be improved.
During the penetration testing process, an individual would be given the authority to deliberately breach the security system. This would be done to determine the vulnerability and then propose the best solutions for computer network protection.
In the penetration testing process, risk assessment would seem like the main objective. After all, this would be used to determine the weaknesses of the security system in several ways. It would examine the security of networked systems and external hosts, including firewall protection software and the computer network systems of servers. It would also be used to evaluate the application security risks that would be coming from proprietary applications. In addition, penetration testing could also be used to examine the internal security risks that would tend to exist in a computer network.
Other than all these, penetration testing could also be used to identify the wireless security vulnerabilities or risks. This test would be conducted in order to examine when the access of the current network would be possible. This would be done through both current and highly developed technologies like mailbox access and VOIP.
As a result, penetration testing seems to have become a highly viable asset for growing companies. This is because it would be successful in providing them with all the necessary information about how the data hacking could be secured. In addition, it would also be highly useful and effective for businesses because it would provide vulnerability reports to business owners which would indicate the most likely issues of data breach locations.
All in all, it could be seen that penetration testing indeed has a significant role to play in the IT world.